How to pass 70-417 exam easily? GreatExam is now here to help you with your 70-417 exam certification problems. Because we are the best 70-417 exam questions training material providing vendor, all of our candidates get through 70-417 exam without any problem.
QUESTION 301
Hotspot Question
You have two servers that run Windows Server 2012 R2.
The servers are configured as shown in the following table.
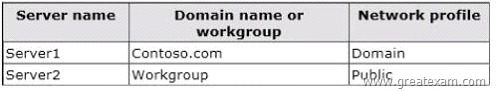
You need to ensure that Server2 can be managed by using Server Manager from Server1.
In the table below, identify which actions must be performed on Server1 and Server2.Make only one selection in each row. Each correct selection is worth one point.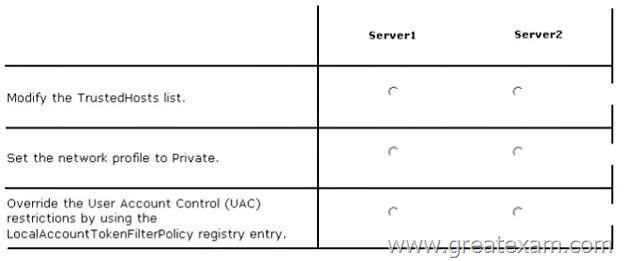
Answer: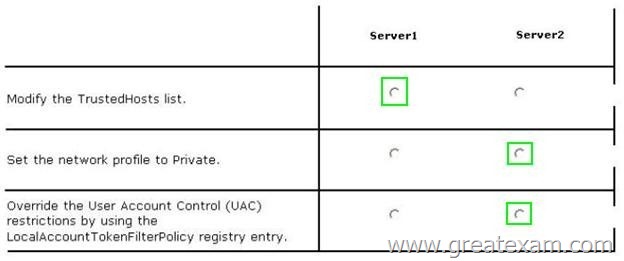
Explanation:
http://technet.microsoft.com/library/hh831453.aspx
QUESTION 302
Your network contains an Active Directory forest named contoso.com. The forest contains a single domain. All servers runs Windows Server 2012 R2.The domain contains two domain controllers named DC1 and DC2.
Both domain controllers are virtual machines on a Hyper-V host.
You plan to create a cloned domain controller named DC3 from an image of DC1.
You need to ensure that you can clone DC1.
Which two actions should you perform? (Each correct answer presents part of the solution.
Choose two.)
A. Add the computer account of DC1 to the Cloneable Domain Controllers group.
B. Create a DCCIoneConfig.xml file on DC1.
C. Add the computer account of DC3 to the Cloneable Domain Controllers group.
D. Run the Enable-AdOptionalFeaturecmdlet.
E. Modify the contents of the DefaultDCCIoneAllowList.xml file on DC1.
Answer: AB
Explanation:
* Cloneable Domain Controllers Group (located in the Users container). Membership in this group dictates whether a DC can or cannot be cloned. This group has some permissions set on the domain head that should not be removed. Removing these permissions will cause cloning to fail. Also, as a best practice, DCs shouldn’t be added to the group until you plan to clone and DCs should be removed from the group once cloning is complete. Cloned DCs will also end up in the Cloneable Domain Controllers group.
* DCCloneConfig.xml is an XML configuration file that contains all of the settings the cloned DC will take when it boots. This includes network settings, DNS, WINS, AD site name, new DC name and more.
QUESTION 303
Your network contains an Active Directory domain named contoso.com.
The domain contains a domain controller named DC1 that runs Windows Server 2012 R2.
DC1 has the DHCP Server server role installed.
DHCP is configured as shown in the exhibit. (Click the Exhibit button.)
You discover that client computers cannot obtain IPv4 addresses from DC1.
You need to ensure that the client computers can obtain IPv4 addresses from DC1.
What should you do?
A. Disable the Deny filters.
B. Authorize DC1.
C. Activate the scope.
D. Disable the Allow filters.
Answer: D
Explanation:
There is no items in the deny List. So it means that client computers MAC addresses is not listed in the allow list. So we have to disable the “Allow Filters”
http://technet.microsoft.com/en-us/library/ee956897(v=ws.10).aspx
QUESTION 304
You have a failover cluster named Cluster1 that contains four nodes.
All of the nodes run Windows Server 2012 R2.
You need to schedule the installation of Windows updates on the cluster nodes.
Which tool should you use?
A. The Add-CauClusterRolecmdlet
B. TheWuauclt command
C. TheWusa command
D. The Invoke-CauScancmdlet
Answer: D
Explanation:
The Invoke-CauScancmdlet performs a scan of cluster nodes for applicable updates and returns a list of the initial set of updates that would be applied to each node in a specified cluster.
http://technet.microsoft.com/en-us/library/hh847235(v=wps.620).aspx
http://technet.microsoft.com/en-us/library/cc720477(v=ws.10).aspx
http://support.microsoft.com/kb/934307
http://technet.microsoft.com/en-us/library/hh847228(v=wps.620).aspx
QUESTION 305
Your network contains an Active Directory domain named adatum.com. All domain controllers run Windows Server 2012 R2. The domain contains a virtual machine named DC2.
On DC2, you run Get-ADDCCloningExcludcdApplicationList and receive the output shown in the following table.
You need to ensure that you can clone DC2.
Which two actions should you perform? (Each correct answer presents part of the solution.
Choose two.)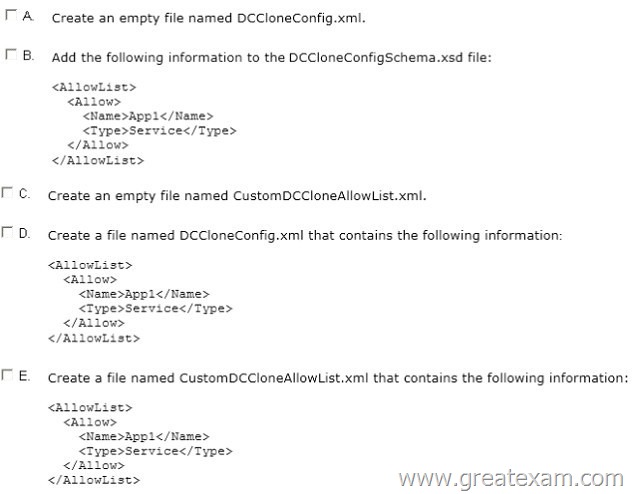
A. Option A
B. Option B
C. Option C
D. Option D
E. Option E
Answer: AE
Explanation:
Because domain controllers provide a distributed environment, you could not safely clone an Active Directory domain controller in the past.
Before, if you cloned any server, the server would end up with the same domain or forest, which is unsupported with the same domain or forest. You would then have to run sysprep, which would remove the unique security information before cloning and then promote a domain controller manually. When you clone a domain controller, you perform safe cloning, which a cloned domain controller automatically runs a subset of the sysprep process and promotes the server to a domain controller automatically.
The four primary steps to deploy a cloned virtualized domain controller are as follows:
Grant the source virtualized domain controller the permission to be cloned by adding the source virtualized domain controller to the Cloneable Domain Controllers group.
Run Get-ADDCCloningExcludedApplicationListcmdlet in Windows PowerShell to determine which services and applications on the domain controller are not compatible with the cloning.
Run New-ADDCCloneConfigFile to create the clone configuration file, which is stored in the C:\Windows\NTDS.
In Hyper-V, export and then import the virtual machine of the source domain controller.
Run Get-ADDCCloningExcludedApplicationListcmdlet In this procedure, run the Get- ADDCCloningExcludedApplicationListcmdlet on the source virtualized domain controller to identify any programs or services that are not evaluated for cloning. You need to run the Get-ADDCCloningExcludedApplicationListcmdlet before the New- ADDCCloneConfigFilecmdlet because if the New-ADDCCloneConfigFilecmdlet detects an excluded application, it will not create a DCCloneConfig.xml file. To identify applications or services that run on a source domain controller which have not been evaluated for cloning Get-ADDCCloningExcludedApplicationList
Get-ADDCCloningExcludedApplicationList -GenerateXml
The clone domain controller will be located in the same site as the source domain controller unless a different site is specified in the DCCloneConfig.xml file.
Note:
The Get-ADDCCloningExcludedApplicationListcmdlet searches the local domain controller for programs and services in the installed programs database, the services control manager that are not specified in the default and user defined inclusion list. The applications in the resulting list can be added to the user defined exclusion list if they are determined to support cloning. If the applications are not cloneable, they should be removed from the source domain controller before the clone media is created. Any application that appears in cmdlet output and is not included in the user defined inclusion list will force cloning to fail.
The Get-ADDCCloningExcludedApplicationListcmdlet needs to be run before the New- ADDCCloneConfigFilecmdlet is used because if the New-ADDCCloneConfigFilecmdlet detects an excluded application, it will not create a DCCloneConfig.xml file. DCCloneConfig.xml is an XML configuration file that contains all of the settings the cloned DC will take when it boots. This includes network settings, DNS, WINS, AD site name, new DC name and more. This file can be generated in a few different ways.
The New-ADDCCloneConfigcmdlet in PowerShell
By hand with an XML editor
By editing an existing config file, again with an XML editor (Notepad is not an XML editor.)
You can populate the XML file. . . . . doesn’t need to be empty. . . . .
http://technet.microsoft.com/en-us/library/hh831734.aspx
http://blogs.dirteam.com/blogs/sanderberkouwer/archive/2012/09/10/new-features-in-active-directory-domain-services-in-windows-server-2012-part-13-domain-controller-cloning.aspx
QUESTION 306
Hotspot Question
Your network contains an Active Directory domain named contoso.com.
The domain contains a server named Server2 that runs Windows Server 2012 R2.
You are a member of the local Administrators group on Server2.
You install an Active Directory Rights Management Services (AD RMS) root cluster on Server2.
You need to ensure that the AD RMS cluster is discoverable automatically by the AD RMS client computers and the users in contoso.com.
Which additional configuration settings should you configure? To answer, select the appropriate tab in the answer area.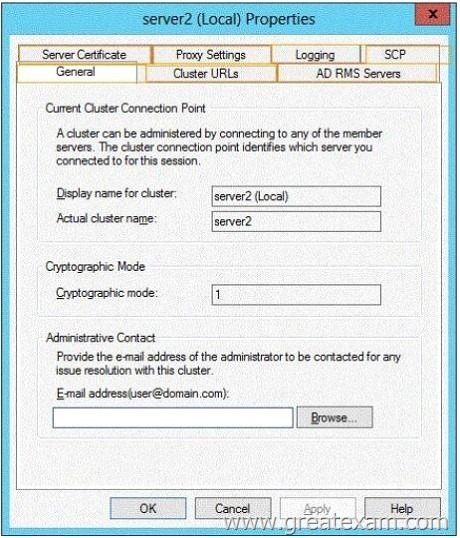
Answer: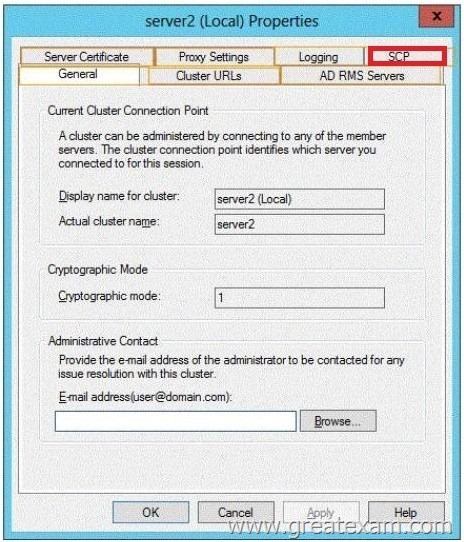
QUESTION 307
Hotspot Question
Your network contains an Active Directory domain named contoso.com. The domain contains a member server named Server1. Server1 runs Windows Server 2012 R2.
You enable the EventLog-Application event trace session.
You need to set the maximum size of the log file used by the trace session to 10 MB.
From which tab should you perform the configuration? To answer, select the appropriate tab in the answer area.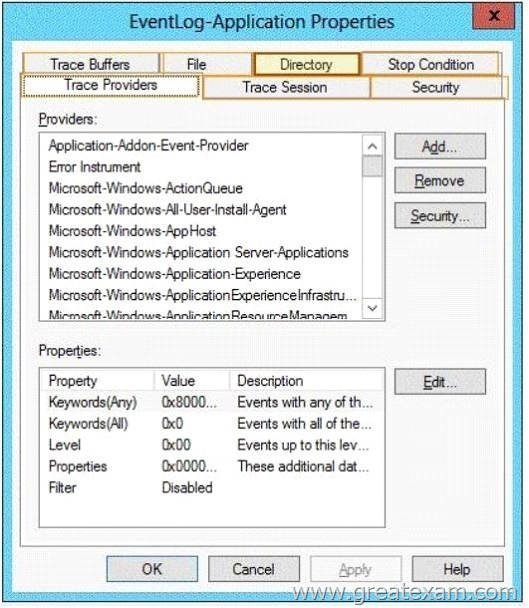
Answer: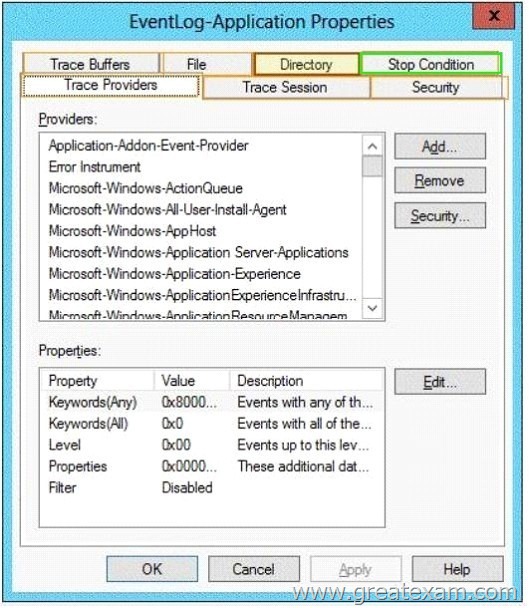
QUESTION 308
Your network contains an Active Directory domain named contoso.com. The domain contains a member server named Server 1. All servers run Windows Server 2012 R2.
You need to collect the error events from all of the servers on Server1. The solution must ensure that when new servers are added to the domain, their error events are collected automatically on Server1.
Which two actions should you perform? (Each correct answer presents part of the solution.
Choose two.)
A. On Server1, create a collector initiated subscription.
B. On Server1, create a source computer initiated subscription.
C. From a Group Policy object (GPO), configure the Configure target Subscription Manager setting.
D. From a Group Policy object (GPO), configure the Configure forwarder resource usage setting.
Answer: BC
Explanation:
To set up a Source-Initiated Subscription with Windows Server 2003/2008 so that events of interest from the Security event log of several domain controllers can be forwarded to an administrative workstation
* Group Policy
The forwarding computer needs to be configured with the address of the server to which the events are forwarded. This can be done with the following group policy setting:
Computer configuration-Administrative templates-Windows components-Event forwarding- Configure the server address, refresh interval, and issue certificate authority of a target subscription manager.
* Edit the GPO and browse to Computer Configuration | Policies | Administrative Templates | Windows Components | Event Forwarding – Configure the server address, refresh interval, and issuer certificate authority of a target Subscription Manager
QUESTION 309
Hotspot Question
Your network contains a RADIUS server named Admin1.
You install a new server named Server2 that runs Windows Server 2012 R2 and has Network Policy Server (NPS) installed.
You need to ensure that all accounting requests for Server2 are forwarded to Admin1.
On Server2, you create a new remote RADIUS server group named Group1 that contains Admin1.
What should you configure next on Server2? To answer, select the appropriate node in the answer area.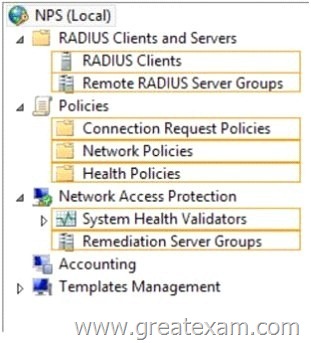
Answer: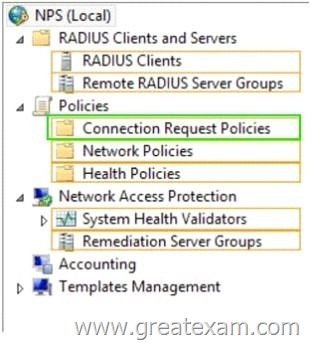
QUESTION 310
Your network contains an Active Directory domain named adatum.com.
A network administrator creates a Group Policy central store.
After the central store is created, you discover that when you create new Group Policy objects (GPOs), the GPOs do not contain any Administrative Templates.
You need to ensure that the Administrative Templates appear in new GPOs.
What should you do?
A. Add your user account to the Group Policy Creator Owners group.
B. Configure all domain controllers as global catalog servers.
C. Copy files from %Windir%\Policydefinitions to the central store.
D. Modify the Delegation settings of the new GPOs.
Answer: C
Explanation:
To take advantage of the benefits of .admx files, you must create a Central Store in the SYSVOL folder on a domain controller. The Central Store is a file location that is checked by the Group Policy tools. The Group Policy tools use any .admx files that are in the Central Store. The files that are in the Central Store are later replicated to all domain controllers in the domain.
QUESTION 311
Hotspot Question
You have a server named Server1 that runs Windows Server 2012 R2. Server1 has the Remote Access server role installed.
You need to configure the ports on Server1 to ensure that client computers can establish VPN connections to Server1 by using TCP port 443.
What should you modify? To answer, select the appropriate object in the answer area.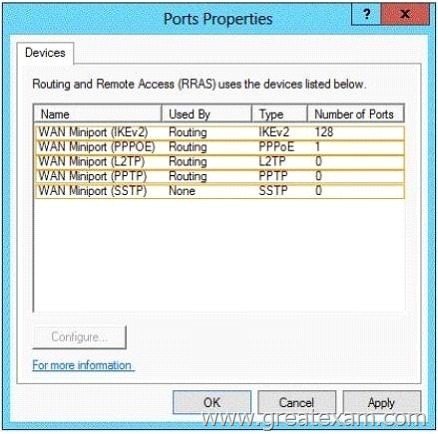
Answer: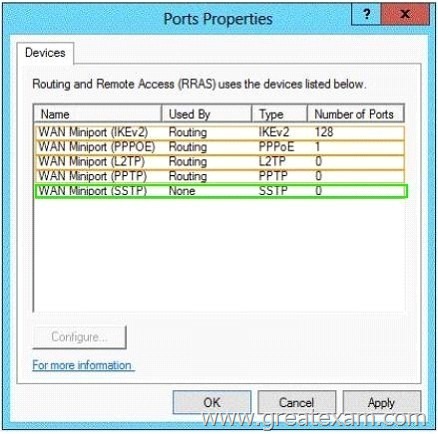
QUESTION 312
Your network contains an Active Directory domain named contoso.com. The domain contains three servers. The servers are configured as shown in the following table.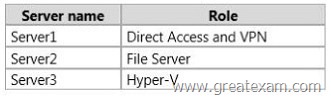
You need to ensure that end-to-end encryption is used between clients and Server2 when the clients connect to the network by using DirectAccess.
Which two actions should you perform? (Each correct answer presents part of the solution.
Choose two.)
A. From the Remote Access Management Console, reload the configuration.
B. Add Server2 to a security group in Active Directory.
C. Restart the IPSec Policy Agent service on Server2.
D. From the Remote Access Management Console, modify the Infrastructure Servers settings.
E. From the Remote Access Management Console, modify the Application Servers settings.
Answer: BE
Explanation:
Unsure about these answers:
A public key infrastructure must be deployed.
Windows Firewall must be enabled on all profiles. ISATAP in the corporate network is not supported. If you are using ISATAP, you should remove it and use native IPv6.
Computers that are running the following operating systems are supported as DirectAccess clients:
Windows Server 2012 R2
Windows 8.1 Enterprise
Windows Server 2012
Windows 8 Enterprise
Windows Server 2008 R2
Windows 7 Ultimate
Windows 7 Enterprise
Force tunnel configuration is not supported with KerbProxy authentication.
Changing policies by using a feature other than the DirectAccess management console or Windows PowerShell cmdlets is not supported.
Separating NAT64/DNS64 and IPHTTPS server roles on another server is not supported.
QUESTION 313
You have a DNS server named DNS1 that runs Windows Server 2012 R2.
On DNS1, you create a standard primary DNS zone named adatum.com.
You need to change the frequency that secondary name servers will replicate the zone from DNS1.
Which type of DNS record should you modify?
A. Name server (NS)
B. Start of authority (SOA)
C. Host information (HINFO)
D. Service location (SRV)
Answer: B
Explanation:
The time to live is specified in the Start of Authority (SOA) record
Note: TTL (time to live) – The number of seconds a domain name is cached locally before expiration and return to authoritative nameservers for updated information.
QUESTION 314
Your network contains an Active Directory domain named contoso.com. The domain contains a member server named Server 1. Server1 has the IP Address Management (IPAM) Server feature installed.
A technician performs maintenance on Server1.
After the maintenance is complete, you discover that you cannot connect to the IPAM server on Server1.
You open the Services console as shown in the exhibit. (Click the Exhibit button.)
You need to ensure that you can connect to the IPAM server.
Which service should you start?
A. Windows Process Activation Service
B. Windows Event Collector
C. Windows Internal Database
D. Windows Store Service (WSService)
Answer: C
QUESTION 315
You have a server named Server1 that runs Windows Server 2012 R2.
Server1 is located in the perimeter network and has the DNS Server server role installed.
Server1 has a zone named contoso.com.
You apply a security template to Server1.
After you apply the template, users report that they can no longer resolve names from contoso.com.
On Server1, you open DNS Manager as shown in the DNS exhibit. (Click the Exhibit button.)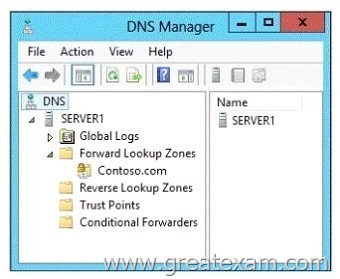
On Server1, you open Windows Firewall with Advanced Security as shown in the Firewall exhibit. (Click the Exhibit button.)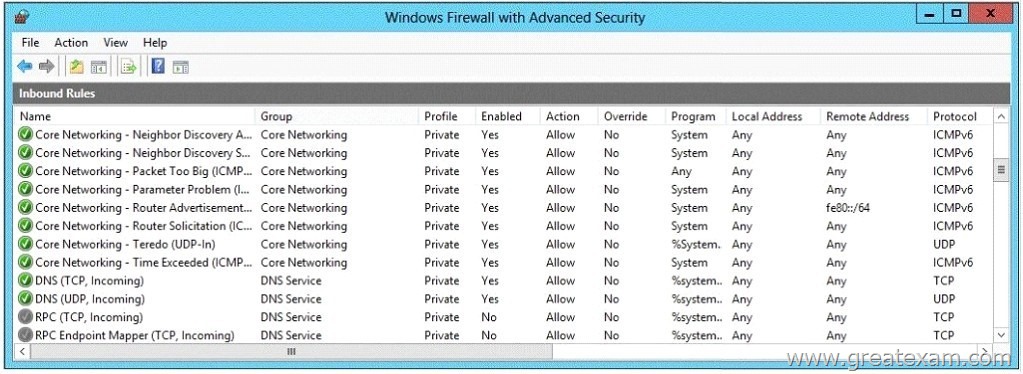
You need to ensure that users can resolve contoso.com names.
What should you do?
A. From Windows Firewall with Advanced Security, disable the DNS (TCP, Incoming) rule and the DNS (UDP, Incoming) rule.
B. From DNS Manager, modify the Zone Transfers settings of the contoso.com zone.
C. From DNS Manager, unsign the contoso.com zone.
D. From DNS Manager, modify the Start of Authority (SOA) of the contoso.com zone.
E. From Windows Firewall with Advanced Security, modify the profiles of the DNS (TCP, Incoming) rule and the DNS (UDP, Incoming) rule.
Answer: E
Explanation:
To configure Windows Firewall on a managed DNS server On the Server Manager menu, click Tools and then click Windows Firewall with Advanced Security.
Right-click Inbound Rules, and then click New Rule. The New Inbound Rule Wizard will launch.
In Rule Type, select Predefined, choose DNS Service from the list, and then click Next.
In Predefined Rules, under Rules, select the checkboxes next to the following rules:
Click Next, choose Allow the connection, and then click Finish. Right-click Inbound Rules, and then click New Rule. The New Inbound Rule Wizard will launch.
etc.
QUESTION 316
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the Active Directory Rights Management Services server role installed.
Your company works with a partner organization that does not have its own Active Directory Rights Management Services (AD RMS) implementation.
You need to create a trust policy for the partner organization.
The solution must meet the following requirements:
– Grant users in the partner organization access to protected content
– Provide users in the partner organization with the ability to create protected content.
Which type of trust policy should you create?
A. A federated trust
B. Windows Live ID
C. A trusted publishing domain
D. A trusted user domain
Answer: A
QUESTION 317
Hotspot Question
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the Active Directory Certificate Services server role installed and configured.
For all users, you are deploying smart cards for logon.
You are using an enrollment agent to enroll the smart card certificates for the users.
You need to configure the Contoso Smartcard Logon certificate template to support the use of the enrollment agent.
Which setting should you modify? To answer, select the appropriate setting in the answer area.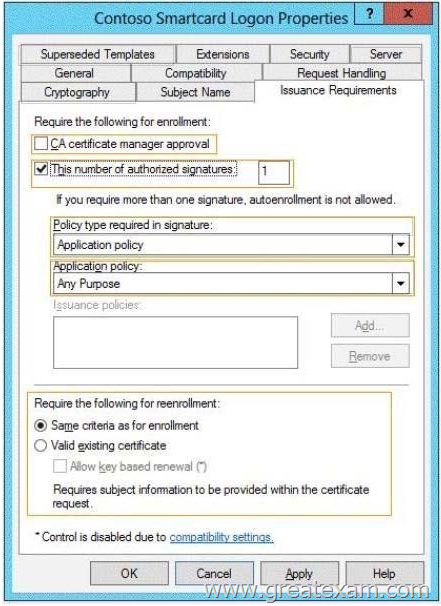
Answer: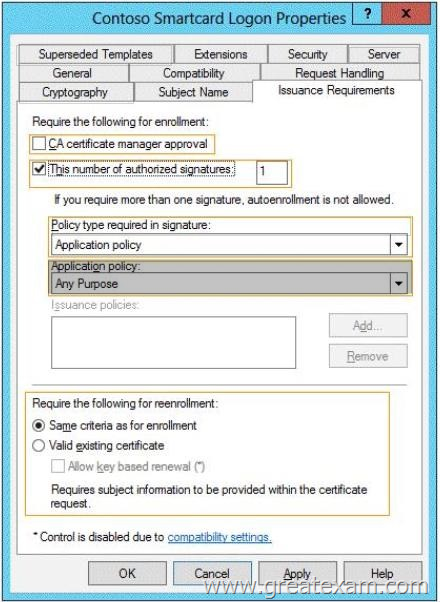
QUESTION 318
Hotspot Question
Your company has a primary data center and a disaster recovery data center.
The network contains an Active Directory domain named contoso.com. The domain contains a server named that runs Windows Server 2012 R2. Server1 is located in the primary data center.
Server1 has an enterprise root certification authority (CA) for contoso.com.
You deploy another server named Server2 to the disaster recovery data center.
You plan to configure Server2 as a secondary certificate revocation list (CRL) distribution point.
You need to configure Server2 as a CRL distribution point (CDP).
Which tab should you use to configure the required CDP entry? To answer, select the appropriate tab in the answer area.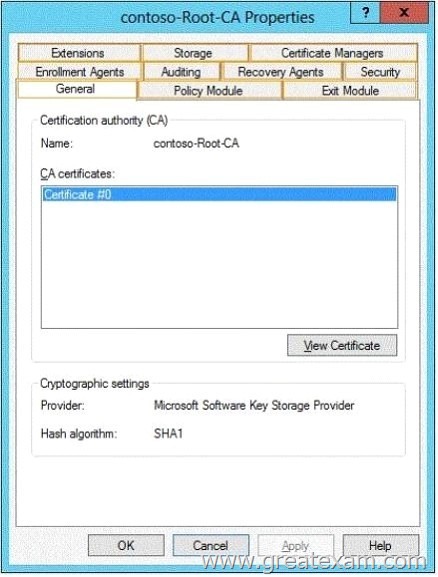
Answer:
QUESTION 319
Hotspot Question
Your network contains an Active Directory domain named contoso.com.
The relevant servers in the domain are configured as shown in the following table.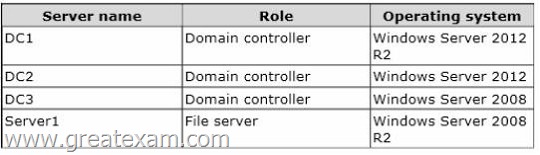
You plan to create a shared folder on Server1 named Share1. Share1 must only be accessed by users who are using computers that are joined to the domain.
You need to identify which servers must be upgraded to support the requirements of Share1.
In the table below, identify which computers require an upgrade and which computers do not require an upgrade. Make only one selection in each row. Each correct selection is worth one point.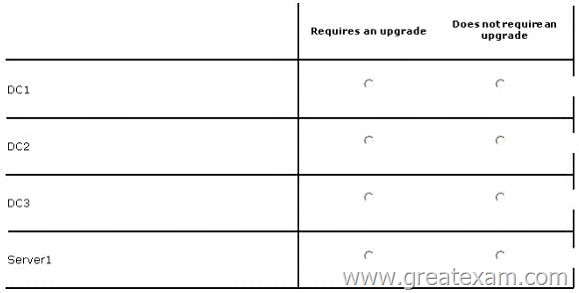
Answer: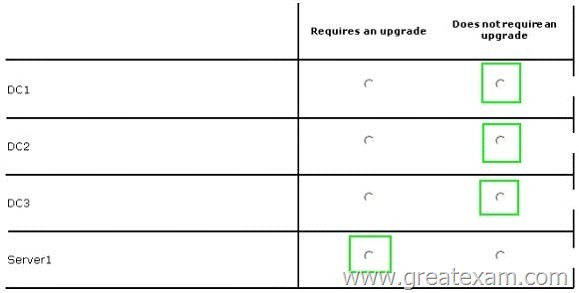
QUESTION 320
Hotspot Question
Your network contains an Active Directory domain named contoso.com.
You have several Windows PowerShell scripts that execute when users log on to their client computer.
You need to ensure that all of the scripts execute completely before the users can access their desktop.
Which setting should you configure? To answer, select the appropriate setting in the answer area.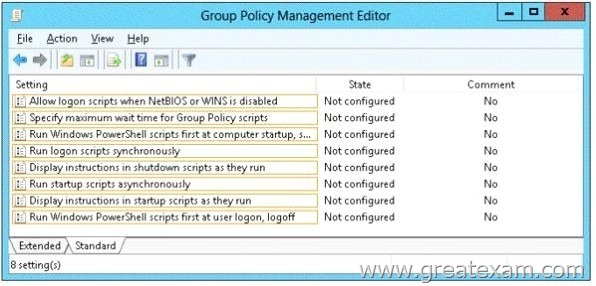
Answer: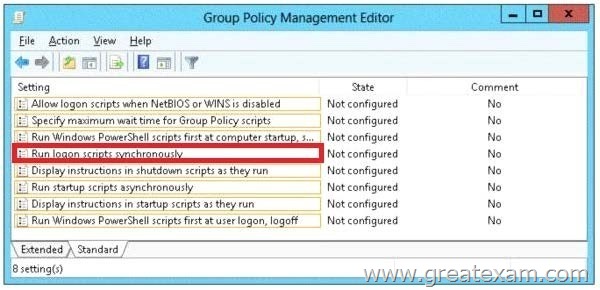
Explanation:
http://technet.microsoft.com/en-us/library/cc738773(v=ws.10).aspx
Run logon scripts synchronously
Directs the system to wait for logon scripts to finish running before it starts the Windows Explorer interface program and creates the desktop.
If you enable this policy, Windows Explorer does not start until the logon scripts have finished running. This setting assures that logon script processing is complete before the user starts working, but it can delay the appearance of the desktop.
If you disable this policy or do not configure it, the logon scripts and Windows Explorer are not synchronized and can run simultaneously.
If you want to get more 70-417 exam study guide, you can download the free 70-417 braindumps in PDF files on GreatExam. It would be great help for your exam. As a professional IT exam study material provider, GreatExam.com gives you more than just exam questions and answers. We provide our customers with the most accurate study guide about the exam and the guarantee of pass. You can easily find 70-417 exam Q&As on our site. All the study guide provided by us are selected by experts in this field. The questions and answers are very easy to understand, and they’re especially great for professionals who have really little time to focus on exam preparations for certifications, due to their work and other private commitments.
http://www.greatexam.com/70-417-exam-questions.html